Awe-Inspiring Examples Of Info About How To Fix Vulnerabilities

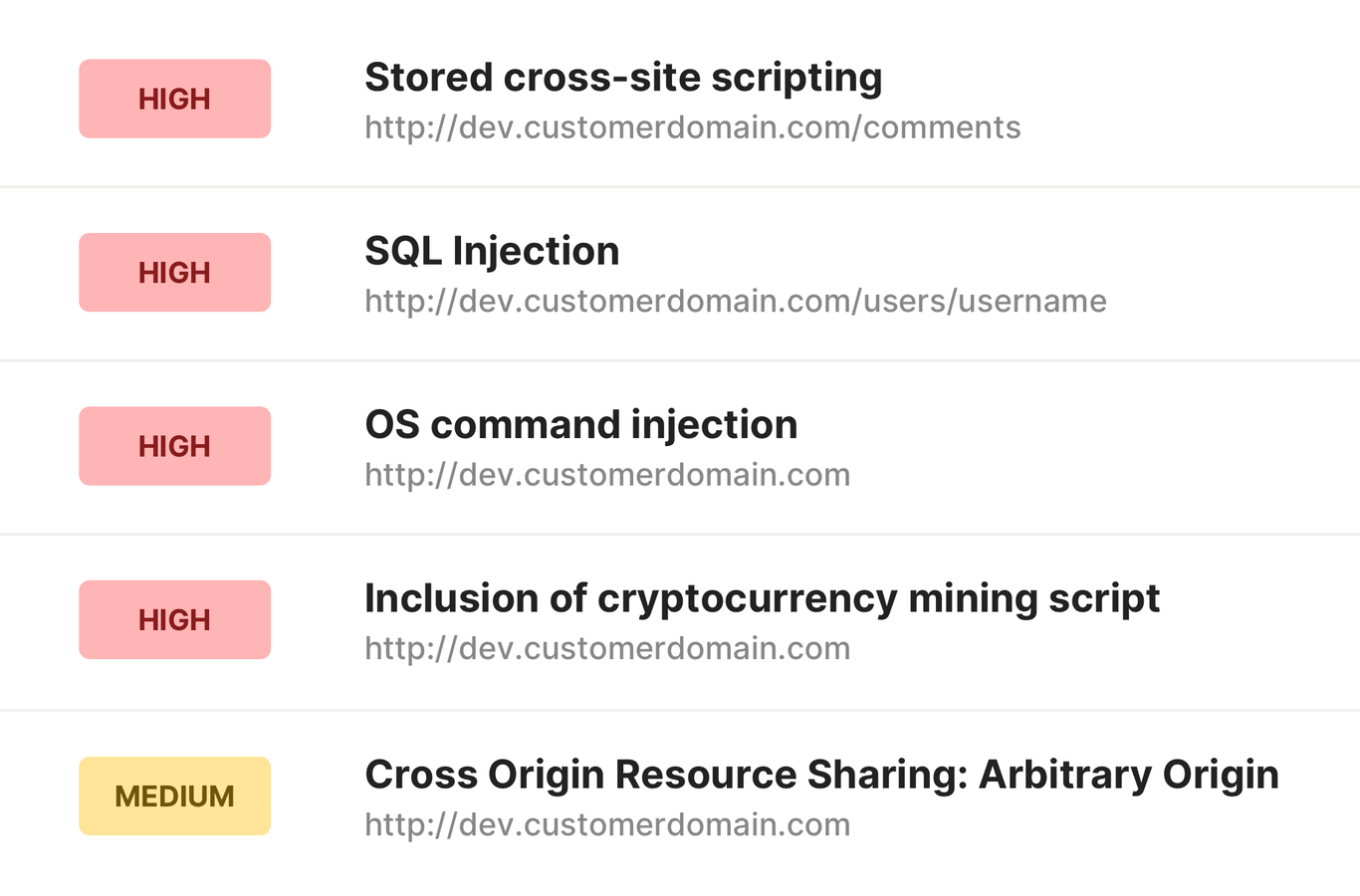
While not necessarily a software vulnerability, this feature can lead to compromises, and should be remediated through the following steps:
How to fix vulnerabilities. Repair the vulnerability, mitigate the risk of the vulnerability, repairing, the most effective way to resolve a vulnerability is to repair it. Ad ncm takes effort out of managing numerous device configurations in a heterogeneous network. 4 hours agobut we are in confusion that why the nessus scan vulnerability shows the tls 1.0 and tls 1.1 protocols even though those 2 protocols are disabled in all possibilities.
Ad find the remote development & it services you need to browse & buy today. Scan your code for vulnerabilities fast. In the upper part of the main application window, click the quarantine link to open the storages window.
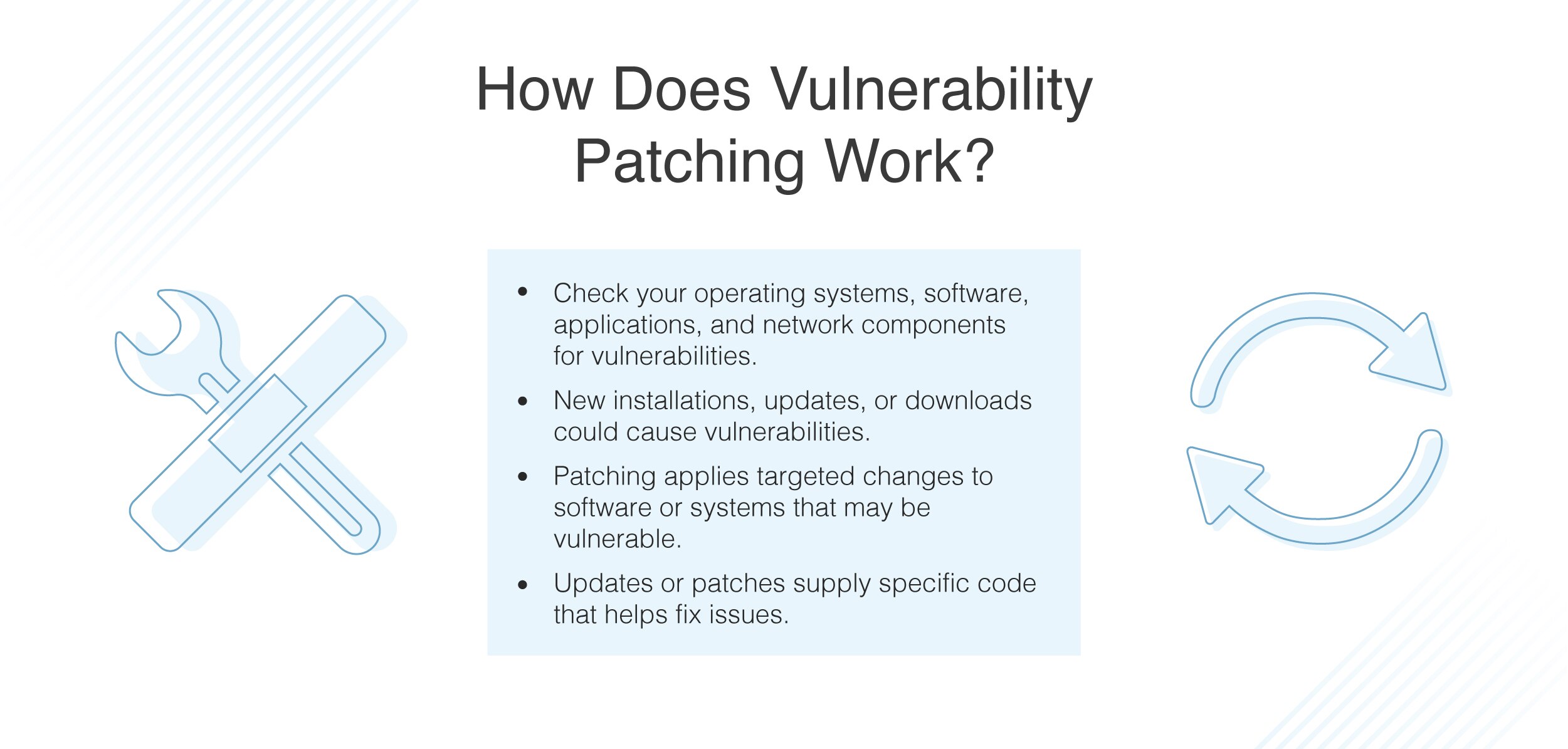
How to fix the new omi vulnerabilities? Fixing vulnerabilities, the third step in the vulnerability remediation process is to fix the weakness. There are few mitigations and fixes available to protect from the new omi vulnerabilities to answer this question.
Security researchers from vectra protect identified a major new vulnerability in microsoft teams, but microsoft says there’s no need for a fix. Open the main application window. Ad check if your software has any open source vulnerabilities with our free scanner.
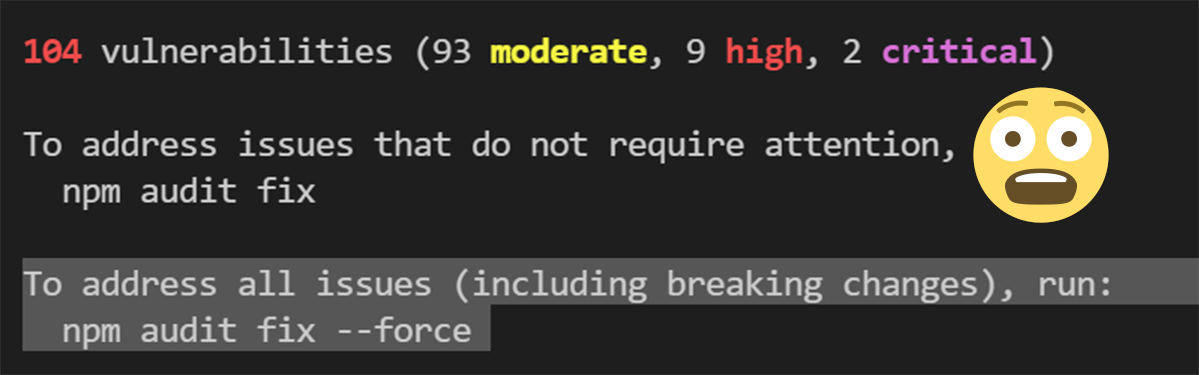
When running npm audit, it says i have 87 vulnerabilities. Ad scan your code against 145,000+ known vulnerabilities. Mitigating, when you mitigate a vulnerability, you attempt.
It can be quite a useful. Ad ncm takes effort out of managing numerous device configurations in a heterogeneous network. Make unauthorized website changes and transactions.
As previously mentioned, there is no yarn audit fix command. The most severe of the vulnerabilities could allow remote code execution if an. Security researchers have recently identified a vulnerability in the microsoft teams desktop app.
To fix the above most common vulnerabilities in java, you will need to identify which of these technologies are used in your environment and visit the respective. Project catalog is the quick and easy way to get more done. See the power of sonatype.
The security flaw could allow attackers to access. Once you click on it, a pr is created on your repository with. In many cases, removing vulnerable software involves deploying an upgrade or a.
Cloudstrike archive scan tool (cast): A universal and easy fix for this issue is to login into your website hosting panel and create an empty file named index.html inside every directory that doesn’t have one. How to quickly find and fix vulnerabilities on windows?







![How To Fix The Top 10 Windows 10 Vulnerabilities [Infographic] | Upguard](https://uploads-ssl.webflow.com/5efc3ccdb72aaa7480ec8179/5f2a2ba11da027ae889f0bfb_top-10-windows-10-security-vulnerabilities-and-how-to-fix-them.jpg)